Introduction: The Compliance Storm is Here
The era of “checkbox security” has reached a strategic inflection point. With the full implementation of the NIS2 Directive, the European Union has transitioned from encouraging voluntary best practices to demanding mandatory operational resilience. For many organizations, this shift feels like a regulatory storm, characterized by a chaotic convergence of supply chain vulnerabilities, granular reporting windows, and the looming shadow of quantum-era threats.
In this landscape, compliance is no longer a secondary administrative task; it is a “regulatory moat” that protects both the organization’s market access and its leadership’s reputation. CYBORA serves as the vital catalyst in this transition, providing the architectural backbone to transform these overwhelming mandates into automated, high-velocity workflows that turn resilience into a competitive advantage.
The Boardroom is Now the Front Line
Under NIS2, cybersecurity has officially graduated from a back-office IT concern to a permanent pillar of boardroom governance. Article 21 mandates that “essential” and “important” entities implement 10 core cybersecurity risk-management measures, ranging from incident handling to “robust cryptography.”
Crucially, the responsibility for these measures sits squarely with top-level management. Boards are now legally required to approve and oversee the implementation of these security protocols. The “surprising reality” that has caught many executives off guard is the introduction of personal liability. Leadership can now face significant sanctions—including potential criminal liability—for gross negligence regarding these obligations.
“Management boards must approve the risk-management measures and oversee their implementation; they can be held liable, including through sanctions, in cases of gross negligence regarding these obligations.” — The NIS2 Directive
CYBORA provides the evidentiary trail required to insulate leadership from this personal liability. By maintaining a historical overview of all risk mitigation efforts, the platform allows management to demonstrate to regulators that they are proactively and diligently overseeing their organization’s security posture.
The 2030 “Quantum Clock” is Already Ticking
While many view quantum computing as a futuristic concept, the NIS2 framework has turned Post-Quantum Cryptography (PQC) into a near-term planning necessity. The primary driver is the “harvest now, decrypt later” threat, where adversaries collect sensitive encrypted data today with the intent of decrypting it once quantum capabilities mature.
The EU has established clear strategic timelines for this transition:
- 2030: Deadline for implementing PQC in critical use cases.
- 2035: Deadline for all other use cases.
Public Key Infrastructure (PKI) is the linchpin of digital trust, yet it is also the most vulnerable to quantum advancement. CYBORA helps organizations “operationalize” this long-term transition through its Secure Digital Signing and PKI support, ensuring that digital signatures and verification processes are updated to meet quantum-resistant standards. By integrating these requirements into its NIS2 Gap Self-Assessment Tool, CYBORA ensures that cryptographic planning is handled as a continuous process rather than a panicked, last-minute project.
Geography is a Security Metric (Non-Technical Risk)
Historically, supply chain security was a technical exercise: checking code for backdoors or hardware for vulnerabilities. However, modern NIS2 compliance introduces the concept of “non-technical risks.” Strategically, a supplier’s jurisdictional exposure and legal environment are now as critical as their software integrity.
This shift is codified in the EU ICT Supply Chain Security Toolbox, adopted on February 13, 2026. This framework represents a massive move from “contractual due diligence” to “regulatory control.” Under this regime, the European Commission is empowered to flag high-risk suppliers or designate entire third countries as cybersecurity concerns.
“The implementation of this toolbox marks a significant shift in EU policy, moving supply chain security from ‘contractual due diligence’ to regulatory control, where the Commission may flag high-risk suppliers.” — The EU ICT Supply Chain Security Toolbox
The implications are boardroom-level: the Commission can now impose binding measures, including prohibitions on data transfers to specific regions or mandating fixed phase-out periods for existing equipment. CYBORA’s automated supplier reviews account for these jurisdictional risks, enabling organizations to perform robust asset mapping and develop the exit plans necessary to remain compliant with shifting EU mandates.
The Death of “Double-Maintenance”
For the thousands of mid-cap enterprises newly classified as “important” entities, the administrative overhead of compliance is the primary threat to operational efficiency. The traditional pain point is “double-maintenance”—the redundant manual entry of the same data across multiple frameworks.
CYBORA eliminates this friction by interconnecting controls across a unified landscape, including:
- NIS2 (Network and Information Security)
- GDPR (General Data Protection Regulation)
- DORA (Digital Operational Resilience Act)
- ISO 27001
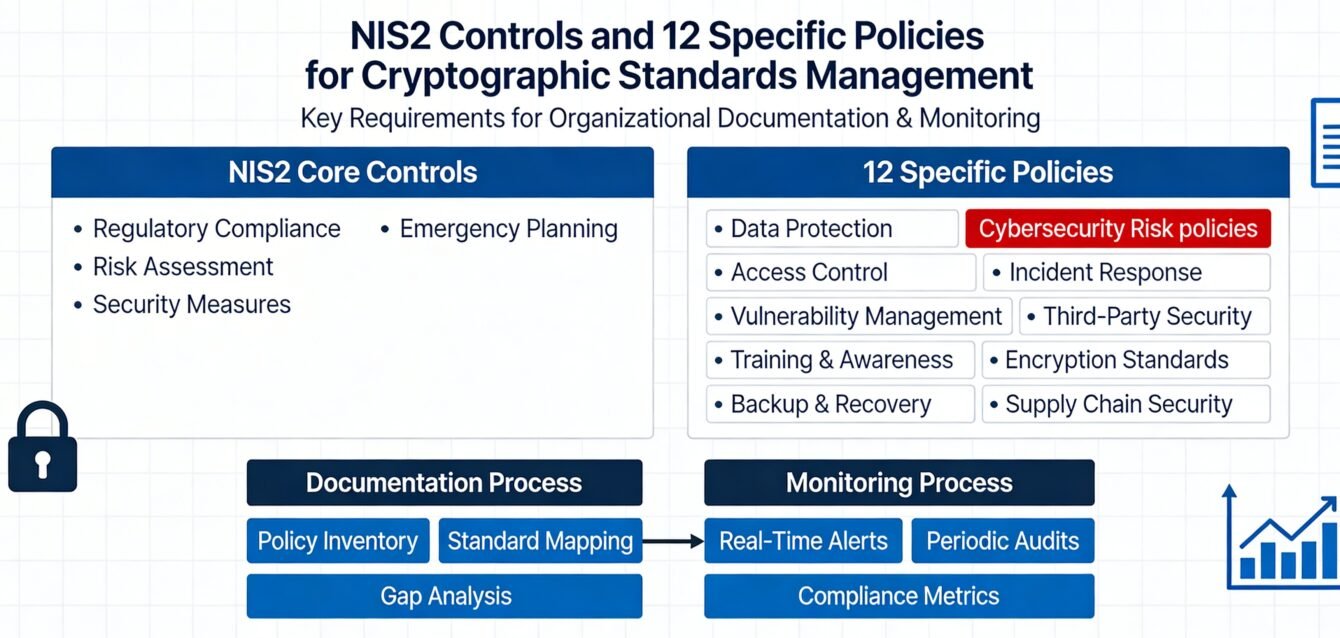
By using CYBORA’s 22 predefined NIS2 controls, 12 specific policies, and 11 recurring tasks, a single update in one area automatically reflects across all connected frameworks.
This efficiency extends to incident reporting. While NIS2 mandates strict 24-hour “early warning” and 72-hour “incident notification” windows, the proposed Digital Omnibus seeks to simplify this through a “single-entry point” for reporting. A key strategic win within this proposal is the potential extension of the personal data breach reporting deadline to 96 hours, providing organizations with the breathing room needed for thorough investigation without sacrificing regulatory transparency.
Trust is Built on a Bill of Materials (SBOM)
Transparency is the new currency of the software supply chain. To combat the rise in sophisticated supply chain attacks, entities are now expected to maintain a Software Bill of Materials (SBOM) for every piece of software they “build and consume.”
An SBOM serves as a comprehensive “ingredient list,” allowing organizations to rapidly identify specific Common Vulnerabilities and Exposures (CVEs) within third-party or open-source libraries. CYBORA standardizes these expectations across the entire supply chain by automating the collection of SBOMs and vendor questionnaires. This moves the organization away from inconsistent, manual inquiries and toward a standardized architecture of digital integrity.
Conclusion: From Compliance to Resilience
The transition to NIS2 is not a one-off administrative exercise; it is a fundamental reconfiguration of business operations for the digital age. Automation, powered by platforms like CYBORA, transforms compliance from a reactive, spreadsheet-based burden into a continuous, proactive process of resilience.
By unifying risk management, incident handling, and supplier oversight, organizations can finally stop managing compliance and start managing risk. As the EU continues its pivot from “contractual due diligence” to “regulatory control,” the strategic question for every leader is no longer if they are compliant, but whether their current framework is robust enough to survive the scrutiny of a new, binding regulatory era.