Declaration of Security Compliance
As of May 1, 2025, the procedures for field testing of power plants (including hybrid systems) and energy storage facilities are changing. If you plan to install or already operate a system with an installed capacity greater than 100 kW, these new requirements apply to you.
Why is this important?
According to the Law on Electricity, the control systems of power plants and energy storage facilities exceeding 100 kW must be secure.
This means these systems cannot be vulnerable to, or remotely controlled from, countries that pose a threat according to Lithuania’s National Security Strategy. The primary goal is to protect against potential attempts to influence power generation processes or alter system parameters from the outside.
What do I need to know before submitting a security declaration?
The audit of the power plant or energy storage facility can only be performed by a supplier (individual or company) that meets all of the following criteria:
Independence: They must be independent—meaning they were not involved in the design, installation, or maintenance of your equipment.
Certification: They must hold an international information systems security audit certification, such as:
ISACA – CISA
ISC² – CISSP
ISO/IEC 27001 Lead Auditor
NKSC Qualification: They must have:
Completed training specified by the National Cyber Security Centre (NKSC);
Passed an exam testing their knowledge and practical skills;
Met the requirements for independence, impartiality, and an impeccable reputation as defined in the NKSC methodology.
We Can Help You Navigate These Changes
Staying compliant with the new security regulations doesn’t have to be a headache. Whether you are currently developing a project or managing an existing facility over 100 kW, our team is ready to assist you in meeting the May 1, 2025 deadline.
How We Assist
Audit Coordination: We can connect you with certified, independent auditors who meet the strict ISACA/ISO and NKSC requirements.
Technical Pre-Assessment: We’ll review your current control systems to identify potential vulnerabilities or links to restricted regions before the official audit begins.
Documentation Management: We help organize and prepare the necessary technical documentation to ensure your Security Compliance Declaration is submitted correctly and on time.
Strategic Advisory: If your hardware or software is found to be non-compliant, we can provide a roadmap for upgrading to secure, compliant alternatives.
Note: Failure to comply with these security standards could lead to delays in commissioning or potential grid disconnection. Getting ahead of the audit process is the best way to ensure operational continuity.
how it worksEverything you need to know about
Artificial Intelligence (AI) is a field of computer science dedicated to creating systems capable of performing tasks that typically require human intelligence. This includes things like reasoning, learning from past experiences, understanding language, and recognizing patterns.
Think of it this way: while traditional software follows a strict “if this, then that” script, AI is designed to process data and make decisions or predictions more dynamically.
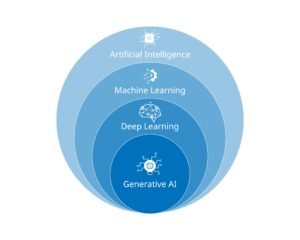
The best way to visualize this is through a “nesting” concept. Machine Learning (ML) is a subset of AI.
AI is the broad vision of machines acting intelligently.
Machine Learning is the specific method used to achieve that vision by training algorithms on large datasets.
This is the “million-dollar question,” and the reality is nuanced. AI is transforming the job market rather than simply erasing it.
Automation: AI is excellent at handling repetitive, data-heavy, or predictable tasks (like data entry or basic customer service).
Augmentation: In most fields, AI acts as a “co-pilot.” It helps doctors diagnose diseases faster or assists coders in writing basic script blocks, allowing humans to focus on high-level strategy and creativity.
New Roles: Just as the internet created jobs like “Social Media Manager,” AI is creating new roles like AI Ethicists, Prompt Engineers, and Data Labelers.
While some displacement is occurring, the historical trend with new technology is that it shifts the type of work humans do rather than eliminating work entirely.
Categorization by Capability
- Narrow AI (Weak AI): Designed for a specific task (e.g., Siri, facial recognition, or Netflix recommendations). This is the only type of AI that currently exists.
- General AI (Strong AI): A theoretical AI that can perform any intellectual task a human can. We aren’t there yet.
- Super AI: A hypothetical level of AI that surpasses human intelligence across all fields.



