I. The Strategic Investment Thesis
CYBORA represents a category-defining shift in the $15B+ Governance, Risk, and Compliance (GRC) market, pivoting the industry from manual, point-in-time audits toward a model of “Continuous Assurance.” While legacy incumbents struggle with “static document mountains” that are obsolete the moment they are printed, CYBORA has engineered an AI-native ecosystem that treats compliance as a living, breathing operational layer. By embedding advanced neural networks into the core of the security stack, CYBORA allows enterprises to move beyond defensive posture into proactive, data-driven resilience.
The CYBORA Vision: Architecting the Future of Trust
- Category Creator in AI-First GRC: Replacing antiquated repositories with a neural architecture that engineers and maintains security frameworks in real-time.
- Radical Moat Construction: Deploying proprietary AI algorithms for behavioral anomaly detection and automated risk scoring, creating a technical barrier to entry that rule-based legacy tools cannot replicate.
- Continuous Governance: Utilizing autonomous AI agents to transition organizations from annual “snapshots” to 24/7 autonomous auditing and policy drafting.
- Transatlantic Strategic Arbitrage: Operating a dual-entity structure that bridges the growing regulatory divergence between the EU and US markets.
The “So What?” for institutional stakeholders is clear: CYBORA is solving the global cybersecurity “skills gap” by providing a synthetic workforce. In a labor market where a qualified CISO commands $250k+ and talent is scarce, CYBORA delivers equivalent governance and oversight at 1/10th the cost and 10x the velocity. This creates an immediate TAM expansion opportunity into the mid-market, where enterprise-grade security was previously cost-prohibitive. This fundamental market imbalance, coupled with a tightening regulatory environment, is the primary driver for CYBORA’s hyper-growth trajectory.
II. The Regulatory Perfect Storm: A Catalyst for Mandatory Demand
Global regulation is no longer a secondary concern; it has become a non-negotiable operational mandate. The shift from “best practice” to “mandatory compliance” (enforced by heavy non-compliance penalties) is driving a surge in demand for automated GRC solutions. CYBORA’s platform is designed to capitalize on this “Regulatory Perfect Storm” by providing the infrastructure required to navigate increasingly complex legal landscapes.
Framework Landscape: Strategic Moats and Market Urgency
| Framework | Region | Primary Urgency & High-Growth Impact |
| EU AI Act | EU | Mandatory compliance for AI systems; a “first-mover” requirement for all tech ventures. |
| NIS2 | EU | Updated security requirements for essential sectors; creates a massive renewal cycle. |
| DORA | EU | Critical operational resilience mandates for the financial services sector. |
| MiCA | EU | Specialized regulation for the crypto-asset market; high barrier-to-entry vertical. |
| AML6 | EU | The sixth Anti-Money Laundering directive; mandatory for financial crime prevention. |
| SOC2 | US | The institutional “gold standard” for SaaS entry into the US enterprise market. |
| NIST | US | Foundational cybersecurity framework required for US federal and private contracts. |
| ISO 27001 | Global | The essential international baseline for information security management. |
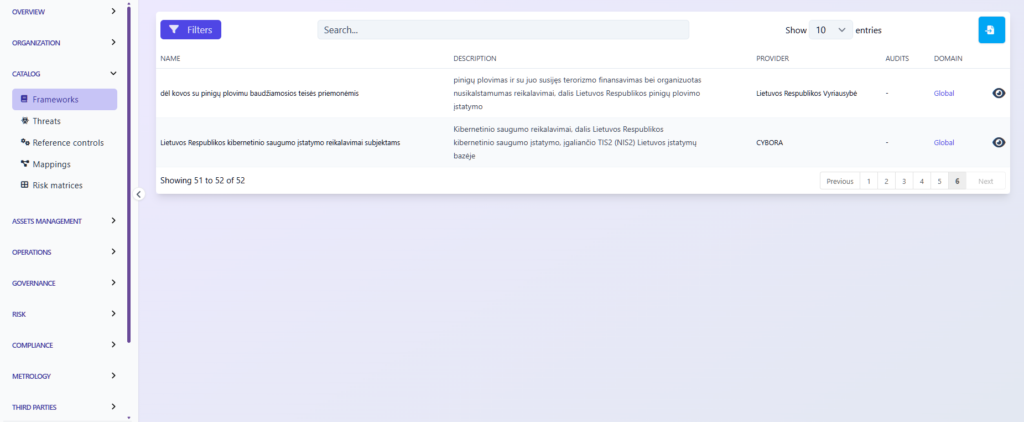
CYBORA currently supports over 62 distinct frameworks, including niche financial and crypto-centric regulations like DORA, MiCA, and AML6. This breadth creates a powerful competitive moat; while niche competitors focus on a single framework, CYBORA acts as a comprehensive “regulatory bridge” for international clients. This expansive coverage ensures predictable, recurring demand as organizations seek a single pane of glass for global compliance.
- ISO 27001:2013 & 27001:2022 🌐
- NIST Cyber Security Framework (CSF) v1.1 🇺🇸
- NIST Cyber Security Framework (CSF) v2.0 🇺🇸
- NIS2 🇪🇺
- SOC2 🇺🇸
- PCI DSS 4.0 💳
- CMMC v2 🇺🇸
- PSPF 🇦🇺
- General Data Protection Regulation (GDPR): Full text and checklist from GDPR.EU 🇪🇺
- Essential Eight 🇦🇺
- NYDFS 500 with 2023-11 amendments 🇺🇸
- DORA (Act, RTS, ITS and GL) 🇪🇺
- NIST AI Risk Management Framework 🇺🇸🤖
- NIST SP 800-53 rev5 🇺🇸
- France LPM/OIV rules 🇫🇷
- CCB CyberFundamentals Framework 🇧🇪
- NIST SP-800-66 (HIPAA) 🏥
- HDS/HDH 🇫🇷
- OWASP Application Security Verification Standard (ASVS) 4 🐝🖥️
- RGS v2.0 🇫🇷
- AirCyber ✈️🌐
- Cyber Resilience Act (CRA) 🇪🇺
- TIBER-EU 🇪🇺
- NIST Privacy Framework 🇺🇸
- TISAX (VDA ISA) v5.1 and v6.0 🚘
- ANSSI hygiene guide 🇫🇷
- Essential Cybersecurity Controls (ECC) 🇸🇦
- CIS Controls v8* 🌐
- CSA CCM (Cloud Controls Matrix)* ☁️
- FADP (Federal Act on Data Protection) 🇨🇭
- NIST SP 800-171 rev2 (2021) 🇺🇸
- ANSSI : recommandations de sécurité pour un système d’IA générative 🇫🇷🤖
- NIST SP 800-218: Secure Software Development Framework (SSDF) 🖥️
- GSA FedRAMP rev5 ☁️🇺🇸
- Cadre Conformité Cyber France (3CF) v1 (2021) ✈️🇫🇷
- ANSSI : SecNumCloud ☁️🇫🇷
- Cadre Conformité Cyber France (3CF) v2 (2024) ✈️🇫🇷
- ANSSI : outil d’autoévaluation de gestion de crise cyber 💥🇫🇷
- BSI: IT-Grundschutz-Kompendium 🇩🇪
- NIST SP 800-171 rev3 (2024) 🇺🇸
- ENISA: 5G Security Controls Matrix 🇪🇺
- OWASP Mobile Application Security Verification Standard (MASVS) 🐝📱
- Agile Security Framework (ASF) – baseline – by intuitem 🤗
- ISO 27001:2013 🌐 (For legacy and migration)
- EU AI Act 🇪🇺🤖
- FBI CJIS 🇺🇸👮
- Operational Technology Cybersecurity Controls (OTCC) 🇸🇦
- Secure Controls Framework (SCF) 🇺🇸🌐
- NCSC Cyber Assessment Framework (CAF) 🇬🇧
- California Consumer Privacy Act (CCPA) 🇺🇸
- California Consumer Privacy Act Regulations 🇺🇸
- NCSC Cyber Essentials 🇬🇧
- Directive Nationale de la Sécurité des Systèmes d’Information (DNSSI) Maroc 🇲🇦
- Part-IS ✈️🇪🇺
- ENS Esquema Nacional de seguridad 🇪🇸
- Korea ISA ISMS-P 🇰🇷
- Swiss ICT minimum standard 🇨🇭
- Adobe Common Controls Framework (CCF) v5 🌐
- BSI Cloud Computing Compliance Criteria Catalogue (C5) 🇩🇪
- Référentiel d’Audit de la Sécurité des Systèmes d’Information, ANCS Tunisie 🇹🇳
- ECB Cyber resilience oversight expectations for financial market infrastructures 🇪🇺
- Mindeststandard-des-BSI-zur-Nutzung-externer-Cloud-Dienste (Version 2.1) 🇩🇪
- Formulaire d’évaluation de la maturité – niveau fondamental (DGA) 🇫🇷
- NIS2 technical and methodological requirements 2024/2690 🇪🇺
- Saudi Arabian Monetary Authority (SAMA) Cybersecurity Framework 🇸🇦
- Guide de sécurité des données (CNIL) 🇫🇷
- International Traffic in Arms Regulations (ITAR) 🇺🇸
- Federal Trade Commission (FTC) Standards for Safeguarding Customer Information 🇺🇸
- OWASP’s checklist for LLM governance and security 🌐
- Recommandations pour les architectures des systèmes d’information sensibles ou à diffusion restreinte (ANSSI) 🇫🇷
- CIS benchmark for Kubernetes v1.10 🌐
- De tekniske minimumskrav for statslige myndigheder 🇩🇰
- Google SAIF framework 🤖
- Recommandations relatives à l’administration sécurisée des SI (ANSSI) 🇫🇷
- Prudential Standard CPS 230 – Operational Risk Management (APRA) 🇦🇺
- Prudential Standard CPS 234 – Information Security (APRA) 🇦🇺
- Vehicle Cyber Security Audit (VCSA) v1.1 🚘
- Cisco Cloud Controls Framework (CCF) v3.0 ☁️🌐
- FINMA – Circular 2023/01 – Operational risks and resilience – Banks 🇨🇭
- Post-Quantum Cryptography (PQC) Migration Roadmap (May 2025) 🔐
- Cloud Sovereignty Framework – 1.2.1 – Oct 2025 🇪🇺
- ISO 22301:2019 outline – Business continuity management systems 🌐
- CCB CyberFundamentals Framework 2025 🇧🇪
- Prestataires de détection des incidents de sécurité (PDIS) – Référentiel d’exigences 🇫🇷
- Vendor Due Diligence – simple baseline – intuitem 🌐
- Points de contrôle Active Directory (AD) – ANSSI 🇫🇷
- ISO 42001:2023 outline – Artificial Intelligence Management System, including Annex A 🤖🌐
- India’s Digital Personal Data Protection Act (DPDPA) – 2023 🇮🇳
- E-ITS (Estonia’s national cyber security standard) – 2024 🇪🇪
- Microsoft cloud security benchmark v1 – ☁️🌐
- Baseline informatiebeveiliging Overheid 2 (BIO2) 🇳🇱
- PGSSI-S (Politique Générale de Sécurité des Systèmes d’Information de Santé) 🇫🇷
- ANSSI : Recommandations de configuration d’un système GNU/Linux 🇫🇷
- PSSI-MCAS (Politique de sécurité des systèmes d’information pour les ministères chargés des affaires sociales) 🇫🇷
- ANSSI : Recommandations pour la protection des systèmes d’information essentiels 🇫🇷
- ANSSI : Recommandations de sécurité pour l’architecture d’un système de journalisation 🇫🇷
- ANSSI : Recommandations de sécurité relatives à TLS 🇫🇷
- New Zealand Information Security Manual (NZISM) 🇳🇿
- Clausier de sécurité numérique du Club RSSI Santé 🇫🇷
- Référentiel National de Sécurité de l’Information (RNSI), MPT Algérie 🇩🇿
- Misure minime di sicurezza ICT per le pubbliche amministrazioni, AGID Italia 🇮🇹
- Framework Nazionale CyberSecurity v2, FNCS Italia 🇮🇹
- Framework Nazionale per la Cybersecurity e la Data Protection, ACN Italia 🇮🇹
- PSSIE du Bénin, ANSSI Bénin 🇧🇯
- IGI 1300 / II 901 – Liste des exigences pour la mise en oeuvre d’un SI classifié (ANSSI) 🇫🇷
- Référentiel Général de Sécurité 2.0 – Annexe B2 🇫🇷
- Recommandations sur la sécurisation des systèmes de contrôle d’accès physique et de vidéoprotection 🇫🇷
- Recommandations pour un usage sécurisé d’(Open)SSH 🇫🇷
- Recommandations de sécurité relatives à IPsec pour la protection des flux réseau 🇫🇷
- Recommandations relatives à l’interconnexion d’un système d’information à internet 🇫🇷
- Guides des mécanismes cryptographiques 🇫🇷
- Swift Customer Security Controls Framework (CSCF) v2025 🏦🌐
- OWASP Application Security Verification Standard (ASVS) 5 🐝🖥️
- NIST 800-82 (OT) – appendix 🏭🤖
- LT TIS2 kibernetinio saugumo įstatymas
- MiCA – Regulation (EU) 2023/1114 of the European Parliament and of the Council of 31 May 2023 on markets in crypto-assets, and amending Regulations (EU) No 1093/2010 and (EU) No 1095/2010 and Directives 2013/36/EU and (EU) 2019/1937 (Text with EEA relevance)
- AML6 – Directive (EU) 2024/1640 of the European Parliament and of the Council of 31 May 2024 on the mechanisms to be put in place by Member States for the prevention of the use of the financial system for the purposes of money laundering or terrorist financing, amending Directive(EU) 2019/1937, and amending and repealing Directive (EU) 2015/849 (Text with EEA relevance)
III. Disrupting Legacy GRC: The AI-First Technical Advantage
Traditional GRC platforms are essentially glorified spreadsheets. CYBORA disrupts this by utilizing an adaptive neural architecture that integrates directly with corporate systems to provide an “honest,” real-time security posture. Unlike rule-based legacy systems, CYBORA’s proprietary algorithms are designed to learn and evolve alongside the threat landscape.
Core Technical Differentiators
- Autonomous AI Agents (Neural Layers): CYBORA employs advanced neural networks that operate 24/7 to execute complex internal audits, policy drafting, and risk mapping, effectively replacing hundreds of manual billable hours.
- Automated Policy Engineering: Using proprietary AI, the platform generates and maintains security frameworks in real-time. This is not a static update; it is an active recalibration based on internal system changes and external regulatory shifts.
- Advanced Threat Intelligence & Detection: CYBORA integrates darknet monitoring (credentials, company exposure), behavioral anomaly detection, and automated risk scoring for suspicious activity. This ensures that GRC is rooted in actual threat mitigation rather than just administrative box-ticking.
The quantified impact on the bottom line is undeniable. CYBORA’s automation delivers a 60–80% reduction in manual workloads and a 50–80% increase in work performance through its AI Service. For the client, this translates to massive ROI by redirecting capital from compliance overhead to core product innovation, all while achieving a superior security maturity level.
IV. The Virtual Security Operator (VSO) Ecosystem
The VSO model is CYBORA’s answer to the mid-market’s need for “Compliance-as-a-Service.” By providing a mobile, scalable virtual security department, CYBORA democratizes elite-level leadership.
The Core VSO Pillars
- vCISO (Chief Information Security Officer): Strategic governance and executive-level risk management across 62+ frameworks.
- vSOC (Security Operations Center): Continuous 24/7 monitoring and incident management to prevent downtime and data loss.
- vDPO (Data Protection Officer): Specialized focus on privacy mandates (GDPR, EU AI Act) and bridging transatlantic data protection gaps.
- vCTO (Chief Technology Officer): Fractional leadership focused on IT roadmaps, digital transformation, and AI adoption strategies.
This model provides on-demand leadership, allowing organizations to scale their security oversight as they grow. By removing the $200k+ per-head salary overhead of internal executive departments, CYBORA provides SMEs with an enterprise-level security posture on a predictable subscription basis, setting the stage for frictionless global expansion.
V. The Transatlantic Bridge: Dual-Market Operational Strategy
To effectively navigate the “Regulatory Perfect Storm,” CYBORA maintains a dual-entity structure that provides unique synergy between the EU and US jurisdictions.
The Regulatory Bridgehead
- CYBORA, MB (EU): Headquartered in Vilnius, this entity manages the complexities of European mandates like the EU AI Act, NIS2, and GDPR.
- CYBORA LLC (US): Specialized in SOC2, NIST, and the high-value US Enterprise market.
This structure allows CYBORA to map security frameworks across disparate jurisdictions, ensuring a single security posture can meet the requirements of both markets simultaneously.
Global Footprint & Due Diligence
- EU Headquarters: Akademijos g. 4, 4th floor, North Wing, Vilnius, Lithuania, LT-08412.
- EU Call Center: +370 640 122 61 (LT).
- UK Support: +44 7482 679489.
- US Operations: Dedicated New York-based call center at +1 917 795 4418.
This established physical and regulatory presence accelerates international market entry for clients, positioning CYBORA as an essential strategic partner rather than just a software vendor.
VI. Commercial Model and Scalable Growth Path
CYBORA’s revenue architecture is built for high-margin, predictable scalability, focusing on maximizing Monthly Recurring Revenue (MRR) across four key pillars:
- SaaS Licensing: High-margin recurring revenue from the core AI GRC Platform.
- Subscription Services: Ongoing retainers for vCISO, vSOC, and vDPO “Compliance-as-a-Service.”
- Enterprise Integration: API-driven automation and custom neural network implementations.
- Regulatory Audits: High-value specialized AI compliance and security auditing.
Sales Enablement and Proof of Concept CYBORA has already demonstrated significant market traction, generating over $50 million in additional revenue for its clients. This was achieved by accelerating enterprise deal closures (reducing the time-to-compliance) and preventing the operational friction and costly downtime associated with security incidents.
Investment Opportunity CYBORA is currently seeking strategic capital to fuel the next phase of its evolution.
- Investment Vehicles: Equity (Minority Stake), SAFE, or Convertible Note.
- Primary Objectives: Accelerating the development of proprietary GRC AI Agents (Product Evolution), scaling sales networks across the EU/US (Market Expansion), and streamlining Enterprise onboarding through key industry certifications.
VII. Value Realization and Exit Strategy
As the AI-GRC category matures, CYBORA is positioned at the intersection of AI, Security, and Regulation—the three most critical spend categories for the modern enterprise. We anticipate a maturation of this sector leading to high-multiple exit opportunities.
Primary Exit Pathing
- Global Consulting Groups (The Big 4): Seeking to shift their low-margin manual auditing hours into CYBORA’s high-speed, automated compliance engine.
- Major Cybersecurity Platforms: Legacy players (e.g., Palo Alto, CrowdStrike) looking to acquire an AI-native compliance layer to complete their “platformization” strategy.
- Enterprise SaaS Consolidators: Growth-equity backed consolidators seeking a “Compliance-by-Design” moat to protect their broader portfolio.
Investor Value Proposition Summary CYBORA offers a high-velocity growth story powered by a proven dual-continent operational structure and a proprietary neural architecture that delivers measurable, multi-million dollar ROI to its clients. By automating the most expensive and labor-intensive aspects of governance, CYBORA is not merely a tool; it is the emerging global standard for AI and cybersecurity management.
Executive Conviction Statement: “If you want to grow through AI securely – you choose CYBORA.”