The new era of NIS2 – from bureaucracy to automated security
With the entry into force of the NIS2 Directive, cybersecurity governance is moving beyond the boundaries of static compliance assessment. For organizations, this means not only stricter requirements, but also the need to reduce the “administrative friction” caused by complex regulatory processes. In this new era, compliance must evolve from a “paper” bureaucracy to operational security. The strategic use of artificial intelligence (AI) is becoming a critical factor in transforming compliance into a dynamic, real-time process.
Many organizations still believe that implementing TIS2 requirements inevitably requires thousands of hours of manual work and huge costs for external consultants. However, AI-powered governance, risk and compliance (GRC) solutions allow for initial compliance to be achieved “in minutes.” This is possible by automating initial vulnerability assessment, task generation and document analysis, freeing security professionals from routine work and allowing them to focus on real threat management.
The bridge between strategic goals and their practical implementation begins with a granular understanding of the current security state.
Smart Analysis: Identifying the current security level and gaps
Objective gap assessment (Gap Assessment) is the foundation of any compliance strategy. Without accurate identification of where an organization’s processes fall short of regulatory expectations, it is impossible to formulate an effective risk management plan.
CYBORA The platform operationalizes this process using a specialized gap self-assessment tool (Gap Self-Assessment Tool), based on 22 specific TIS2 control mechanisms. AI’s ability to automatically analyze internal documents and policies allows it to instantly detect discrepancies between the current state and the requirements of the directive, thus eliminating errors in subjective assessment.
In accordance with Article 21 of the TIS2, the platform helps to ensure compliance 10 essential cybersecurity risk management tools:
- Risk management and analysis: general threat identification strategies.
- Incident management: procedures to ensure reporting and management.
- Business continuity: backup management, disaster recovery and crisis management.
- Supply chain security: ensuring relationships with direct suppliers.
- Network and information systems security: security in the acquisition and development of systems.
- Cyber hygiene practices: zero confidence (Zero-trust) principles and software updates.
- Use of cryptography: implementing strong encryption standards.
- Human resources security and access control: asset management and access policies.
- Multi-factor authentication (MFA): multi-layered identity verification solutions.
- Cybersecurity training: continuous education of employees and management.
Identified internal gaps become the basis for further actions, especially in managing critical supply chain risks.
Supply Chain Security Automation: From Questionnaires to Risk Management
Modern cyberattacks increasingly target supply chains, shifting regulatory focus from “contractual due diligence” to strict “regulatory control.” This is evidenced by February 13, 2026 accepted EU ICT supply chain security toolbox (EU ICT Supply Chain Security Toolbox), which introduces a standardized approach to risk assessment.
CYBORA transforms supplier reviews (Supplier Reviews) through automated workflows (automation-workflows) and 11 predefined recurring tasks (recurring tasks). An important technological advantage is the software specifications (SBOM – Software Bill of Materials) support, allowing for transparent identification of vulnerabilities in third-party components.
| Function | Traditional manual questionnaires | CYBORA automated solutions |
| Efficiency | Fragmented process, high administrative burden. | Fast process through centralized workflows. |
| Standardization | Inconsistent, unclear questions to suppliers. | Standardized expectations according to EU guidelines and SBOM integration. |
| Monitoring | Data in isolated spreadsheets. | Centralized monitoring and API integration into the tech-stack. |
| Jurisdictional risk | Non-technical risks are often ignored. | Jurisdictional exposure and non-technical risk of suppliers are assessed. |
Operational data from supplier assessments is directly integrated into the mandatory compliance documentation.
Automation of documentation and incident management
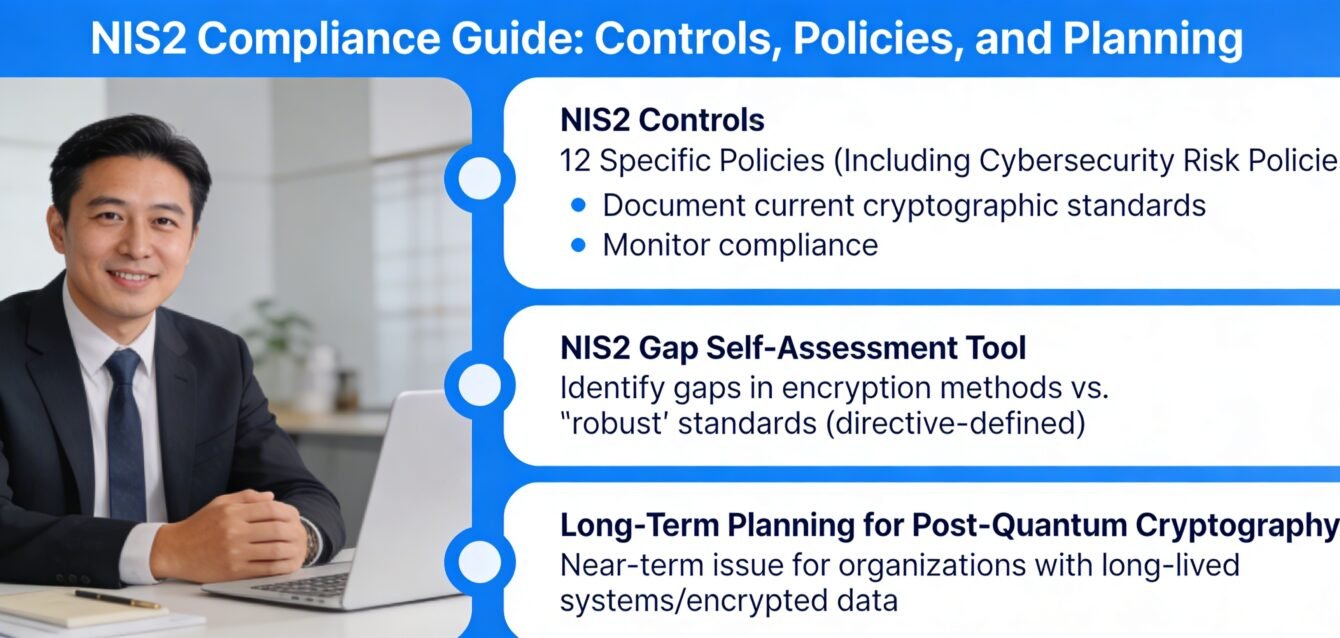
Article 21 of the TIS2 requires real-time reporting, which is not possible without structured governance. CYBORA the system automatically generates 12 TIS2 aligned policies (e.g., cybersecurity risk policy) that become the basis for all security processes.
In the area of incident management, AI helps manage tight deadlines. While the standard NIS2 requirement requires an initial notification within 24 hours and a final notification within 72 hours, the system also takes into account ‘Digital Omnibus’ the nuances of the proposal, which in certain cases (e.g. personal data breaches) may extend the deadlines up to 96 hours through the ‘one-stop shop’ principle.
Main advantages:
- ‘Double Care’ (Double-maintenance) repeal: When controls are updated in the CYBORA system, changes are automatically propagated to related standards (ISO 27001, GDPR, DORA).
- Synchronization of CSIRT activities: Assignment of tasks to incident investigation teams (CSIRTs) and resolution monitoring takes place on a unified platform.
- Centralized reporting: A historical overview of risk mitigation efforts facilitates audit processes.
Effective incident management and documentation are directly related to the strategic responsibility of management.
Strategic Readiness: Board Accountability and the Future of PQC
One of the most significant changes in TIS2 is the personal liability of management. For non-compliance or “gross negligence”, managers can be subject to not only administrative, but also criminal sanctions. Therefore, it is essential for board members to have continuous access to the history of risk mitigation efforts, which is provided by CYBORA.
Strategic planning also includes preparing for post-quantum cryptography (PQC). To protect against ‘collect now, decrypt later’ (harvest now, decrypt later) type attacks, PQC becomes a priority in the near future. The deadlines set by the EU are clear: 2030 for cases of special importance and 2035 for lower risk entities. AI helps integrate these long-term goals into annual risk assessment tasks today.
This strategic preparation is essential in adapting global requirements to the local market.
NIS2 Compliance in Lithuania: From Small Businesses to Critically Important Entities
As Lithuania transposes TIS2 into national law, thousands of entities will be brought under the regulatory umbrella for the first time. This is particularly relevant for medium-sized enterprises (Mid-caps), which may not have large security departments.
CYBORA advantages for Lithuanian organizations:
- Lithuanian language support: simplifies task management and documentation for local teams.
- Resource optimization: 11 recurring tasks framework as allows small teams to act like large security units.
- Compliance with national authorities: The simplified incident reporting format meets the expectations of national CSIRTs.
Three insights for ‘important’ entities:
- Security is a board issue: Delays in implementing controls may result in personal liability for negligence.
- Supplier risk management is mandatory: use SBOM and automated questionnaires to build trust.
- Automation is a resource multiplier: Stop managing compliance in spreadsheets; AI is the only way to manage 22 controls without errors.
Conclusion: Continuous monitoring as a competitive advantage
Artificial intelligence transforms TIS2 compliance from a one-time audit to an ongoing, dynamic process. This allows organizations to not only meet legal requirements, but also gain a real competitive advantage by strengthening digital resilience.
We encourage organizations not to be afraid of the complexity of TIS2, but to exploit the automation opportunities provided by AI to reduce costs and standardize processes. In today’s business environment, digital resilience is not only a legal obligation, but also a stable foundation for business growth.